RealIZM blog series »Hardware security« – Part 2
Making sure that electronic components and assemblies are genuine and fully traceable through their production chain, the researchers active in the SiEvEI 4.0 project are putting several protection mechanisms to use. Among them, a private key infrastructure (PKI) is used to secure the data and structures and create a strong chain of trust (CoT)
Steve Voges, process development engineer and Karl-Friedrich Becker, Group Manager Assembly & Encapsulation at Fraunhofer IZM, have met RealIZM to explain how trustworthy value chains can be created in microelectronics manufacturing. The RealIZM team was also invited to experience the demo production line at Fraunhofer IZM and record the active production line at Siemens on video.
What is the aim of the SiEvEI 4.0 project?
Karl-Friedrich Becker: The project’s title stands for “Safe and intelligent electronic systems for trustworthy electronic products in Industry 4.0”. It’s a joint project that is trying to answer the question of how manufacturing and production environments, equipment, materials, safety issues, and products for industrial applications can be digitally combined. One aim of the project was to develop a concept for tamper-proof traceability for the production chains of electronic assemblies and components.
What does it take to make sure that electronic components are authentic and traceable?
Steve Voges: Our security concept is based on the concept of a chain of trust (CoT). All those involved in production have their own certificate, which they use to identify themselves. This means that all employees on the production line have a personal dongle with a certificate. Each individual machine or infrastructure device that contributes to the CoT also have their own certificate. These certificates are like a personal ID card, and a private key infrastructure (PKI) is used to verify and provide the certificates.
What is special about these certificates, and how do they contribute to hardware security?
Steve Voges: We all known authenticity markers from our everyday lives. Think of watermarks and fluorescent ink on banknotes. But these are not suitable for hardware. In the SiEvEI 4.0 project, we used certificates as a security feature. The certificates act like fingerprints that can be verified using a PKI: A certificate always consists of a private key and a public key. The private key, which is secret, can be used to sign the data. And anyone can check the signature with the public key.
What is the chain of trust all about?
Steve Voges: The chain of trust refers to the tamper-proof linking of each individual process step and associated parameters during production. The key point here is that each link in the chain is “married” to a later process step with the help of the signature, in the form of a certificate. This results in a chain of signed process steps, all stored continuously. This means that each certificate of each machine and person involved is documented and stored in the security chip for offline verification of the CoT.
How did Fraunhofer IZM contribute to forging that Chain of Trust?
Steve Voges: Our task was to install the sensor infrastructure and to design, install, and test the CoT infrastructure for our demo production line. In other words, we determined which machines and people involved needed a certificate. As a result, we were able to prove that the CoT concept works both on our prototype line and on an actual Siemens production line.
Typically, the manufacturing of electronic components does not happen in one place, but is actually distributed. Was this fact taken into account in the project?
Karl-Friedrich Becker: Correct, we also successfully implemented the CoT concept in distributed production. To do this, we initially manufactured some of the electronic assemblies at our research institute. atg Luther & Maelzer GmbH then carried out the incoming inspection by means of electrical testing and placed a first valid stamp on the PCBs. This marked the start of the CoT. The PCBs were then handed over to Siemens CT for further processing and finally taken back to us to have them finalized.
The production of electronic components generates a lot of data from different sources. How did you manage this mass of data?
Steve Voges: We started by structuring and homogenizing the available data with our partner Siemens. Together with our partners Sensorik-Bayern GmbH, Siemens Technology (T), and Bielefeld University, we then designed and installed an infrastructure for sharing that data. As an expert in software licensing, our project partner WIBU-SYSTEMS AG managed, controlled, and designed secure communication between the players involved within the CoT. This allowed us to draw on an established PKI infrastructure system.
Who has access to the CoT?
Steve Voges: In production and later in actual application, the certificate is checked using automatic NFC readers. Each certificate is read and checked for their validity. Specifically, it is checked whether the hash value of the last CoT entry – i.e. the digital fingerprint – is still correct. If even a single bit is changed, the hash value will change. This detection method can be used to prove that the CoT has been tampered with. It is not immediately clear how or where the manipulation took place. Nevertheless, knowing that an electronic component has an invalid code is sufficient to exclude it from further production.
The importance of closed supply chains is emphasized time and again. How were the supply chains structured in the SiEvEI 4.0 project?
Steve Voges: In our joint project, we had an open supply chain. However, it was important that all stakeholders contributing to the CoT had to be part of the PKI. They had to implement and use the PKI and contribute to it with their processes. Depending on the use case, we have to ask how deeply the PKI should be implemented.
In the project, we started at the level of the printed circuit board (PCB). The PCBs were produced here at the research institute and then sent on to atg Luther & Maelzer GmbH. The experts for high-tech test systems checked the PCBs at the beginning and placed a first valid stamp on them. Theoretically, it is conceivable that this process could start even earlier, for example at material suppliers. In other words, the basic material is already provided with its own CoT.
Creating a CoT seems to involve a certain effort. For which areas of application is such a process worthwhile?
Karl-Friedrich Becker: In our SiEvEI 4.0 project, the focus was on the decentralized production of safety-relevant electronic assemblies, e.g. for use in control stations for power plants or in the automotive and aerospace sectors. In principle, the CoT approach is suitable wherever documentation regulations such as ISO 9001 apply or where safety certificates for electronic hardware are mandatory.
What were the biggest challenges for Fraunhofer IZM in the project?
Steve Voges: We were able to demonstrate that code is written automatically in production and that manual processes can also be recorded in our test environment. As already mentioned, we have expertise in which parameters are involved in which processes. We can assess what is relevant and how the interaction with parameters from other processes affects the entire process chain.
How did the project partners succeed in digitizing the production processes and operating procedures and making them usable for industrial applications?
Steve Voges: Basically, a huge amount of data is generated during production. Until now, this information was never stored in the format that is currently required, or only to a limited extent. Together with our project partners, we set up an infrastructure on the data level to not only collect data, but also to organize, structure, and standardize it.
Karl-Friedrich Becker: The standardization of the data is a basic prerequisite for creating meaningful evaluations using machine learning (ML) methods. Preparing the data in a standardized, machine-readable form is essential for AI to be able to work with it in any meaningful way. The Research Institute for Cognition and Robotics (CoR-Lab) at Bielefeld University was responsible for the AI-supported analysis of the data.
What insights did the data analysis provide?
Steve Voges: Thanks to the AI evaluation, we were able to identify process optimizations for our demo production line. For example, based on the recorded process data, it was possible to check specific the areas of components during X-ray analysis where errors were most likely to occur according to the AI. In this way, data evaluation allows for more targeted and efficient oversight.
»Here at Fraunhofer IZM, we have very good process knowhow that is needed to create digital process models. This means we can describe processes, interpret sensor and process data, and establish cross-connections to other processes. With our expertise, we can assist our clients in examining their processes for possible parameters and put forward proposals for deriving data structures for internal processing and enabling automated data evaluation with AI.«
Karl-Friedrich Becker, Group Leader »Assembly & Encapsulation«, Fraunhofer IZM
The proliferation of networked, digital, and automated technologies affects all aspects of business life, including the manufacture of microelectronic products. The BMBF-funded joint project SiEvEI 4.0 explores the question of how manufacturing and production environments, equipment, materials, safety questions, and products for industrial applications can be digitally unified. In our RealIZM Tech Insight, we provide a live insight into the research project:
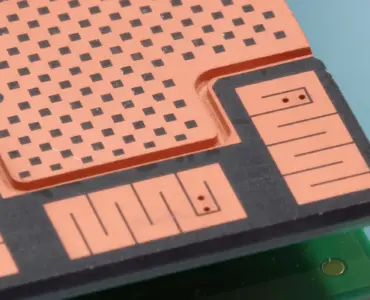
SiEvEI 4.0 State Monitoring Sensor Systems for Assemblies | © Fraunhofer IZM
What contribution could AI evaluations make to hardware security in future?
Karl-Friedrich Becker: In future, we could imagine AI answering the following questions: Was the manufactured product produced with the appropriate process parameters and does the product have the expected service life? If the answer is no, the electronic component would be excluded from further production and would not be used anymore.
In the follow-up project AdaPedge, we and our project partners are exploring the idea of AI evaluation in greater depth. Specifically, one of the aims is to create a self-sufficient sensor mesh network for the production environment in which data is collected and evaluated with AI in addition to the machine data.
Thank you for these exciting insights!
SiEvEI 4.0
Duration: 03/2020 – 08/2023
Funding body: Federal Ministry of Education and Research
Funding reference: 16ME0005
Website: www.elektronikforschung.de/projekte/sievei-4.0
Project partners: Siemens AG (network coordinator), Sensorik-Bayern GmbH, WIBU-SYSTEMS AG, Wagenbrett GmbH & Co. KG, Fraunhofer IZM, Technische Universität Berlin, Bielefeld University and atg Luther & Maelzer GmbH (associated partner)
Update: This article was updated on the 6. of March, 2026.




Add comment